Continued from Part 2
Part 3: Security and Access Control Technology Through the Lens of Human Needs
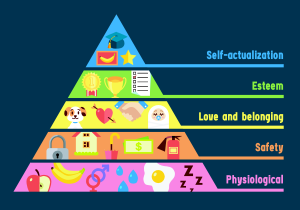
Today, Maslow’s pyramid is so ubiquitous that most people are at least vaguely familiar with the concept. In an article reviewed by clinical psychologist David Susman, Cherry argues that, “Maslow’s hierarchy of needs is one of the best-known theories of motivation.” Unlike many of his peers at the time who were more concerned with the elimination of bad behaviors, “Maslow was much more interested in learning about what makes people happy and the things that they do to achieve that aim.” He outlined five levels: physiological, safety, love and belonging, esteem, and self-actualization. In its original description, each level provides a method for accomplishing goals through maximizing the potential for growth. The idea was that once one’s “basic needs” were met, happiness becomes more dependent on fulfilling higher level desires. “As people progress up the pyramid, needs tend to become increasingly psychological and social.” It should be noted that even from the beginning Maslow was aware that that these levels are less a true hierarchy and more resources that deepens one’s toolkit for growth. For example, he warned that, “the order in which these needs are fulfilled does not always follow this standard progression.”[1]
His more holistic approach to human desire and happiness beyond the removal of ‘bad actors’ makes it such a useful tool for our current discussion. We need a well-rounded security plan that still fosters the growth of our different communities. Hopper, a doctor of psychology, argues that Maslow emphasized “fulfillment” while recognizing that we may not be able to completely meet one need before moving on to the next. Since the time Maslow’s ‘theory’ was released, decades of research backs up its general understanding, as well as reaffirming that it is not so much of a set path where each step is a prerequisite to the next, and “more of a rough guide than a strict rule.” Other researchers have also sought to further refine what Maslow means by self-actualization to include deeper existential questions like “feeling purpose and meaning,” beyond just a potential for growth.[2]
Diener, a social psychologist for the Gallup Organization, recently performed a worldwide survey that agrees with Maslow’s assessment that human needs are universal, but argues that his “ordering” was wrong; instead, we should see each of these ‘levels’ as necessary “ingredients.” Akin to “vitamins,” in his view, “we need them all.” This means that any organizational planning demands that “leaders need to think about them from the outset.”[3] The real importance of Maslow’s approach was to provide a deeper insight to what humans need and their psychological well-being.
This brings us full circle to the criticism of current methods for comparing accessing control and security technologies. Most are too narrowly contained within the first two levels or components of human needs and growth potential, the physiological and safety, without a larger realization of the importance of individual and social growth to the smooth functioning of groups of people as they interface with their security systems. This is not to deny the importance of response volumes or more effective “intrusion detection,” but instead asks how we can have a better way of taking into account all of the different needs people have in today’s modern environments.[4] If we really want to “future proof” our security systems, then they must be flexible and open enough to changing circumstances and requirements.[5] If the COVID-19 pandemic will force a “fundamental rethink” of our entire “ecosystem,” then we need to make sure that includes one that fosters productive social interactions while allowing for the individual to thrive as well.[6] This next section will define what such a methodology could look like.
Continued in Part 4
Endnotes
[1] Cherry, Kendra. “The 5 Levels of Maslow’s Hierarchy of Needs.” Very Well Mind. June 03, 2020. https://www.verywellmind.com/what-is-maslows-hierarchy-of-needs-4136760 (accessed June 22, 2020).
[2] Hopper, Elizabeth. “Maslow’s Hierarchy of Needs.” Thought Co. February 24, 2020. https://www.thoughtco.com/maslows-hierarchy-of-needs-4582571 (accessed July 15, 2020).
[3] Villarica, Hans. “Maslow 2.0: A New and Improved Recipe for Happiness.” The Atlantic. August 17, 2011. https://www.theatlantic.com/health/archive/2011/08/maslow-20-a-new-and-improved-recipe-for-happiness/243486/ (accessed July 15, 2020).
[4] Zhang, Nan, Mark Ryan Dimitar Guelev. “Evaluating Access Control Policies Through Model Checking.” International Conference on Information Security. ISC 2005: Information Security. Singapore, September 20-23, 2005. 446-460.
[5] Liguori, Joseph. “Choosing An Access Control System.” Facility Executive. February 21, 2018. https://facilityexecutive.com/2018/02/facility-security-choosing-access-control-system/ (accessed July 7, 2020).
[6] Rajpal, Nikhil. “Marching Into a Contactless World.” The Economic Times – India. May 13, 2020. https://economictimes.indiatimes.com/blogs/et-commentary/marching-into-a-contactless-world/ (accessed May 28, 2020).